Paper Title: Secure migration patterns from Java 8 to Java 17 in the mission-critical ecosystem: a risk-driven approach to modernization
Authors: Sravan Reddy Kathi, Parth Joshi, Vani Muralidhar, Ajay Venugopalan
Corresponding Author: Sravan Reddy Kathi (sravanreddykathi55@gmail.com)/USA
Abstract
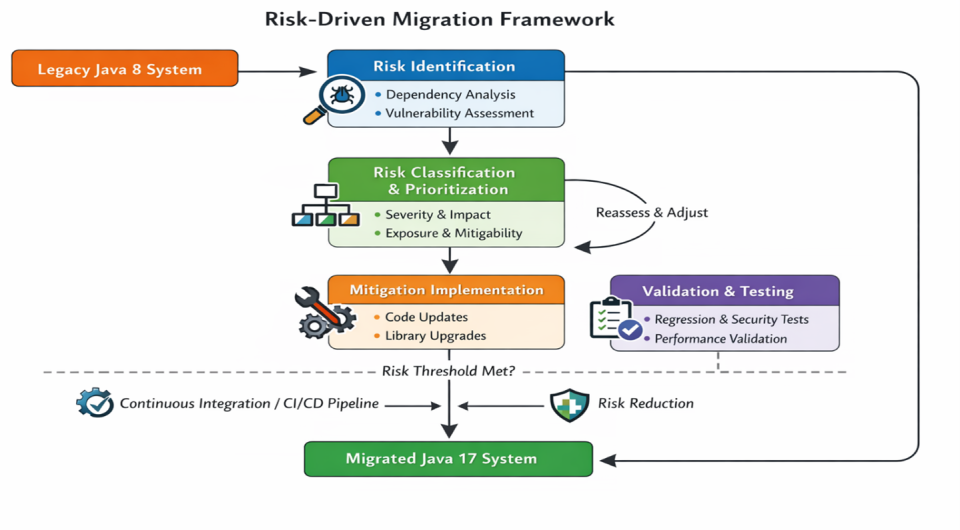
Upgrading from Java 8 to Java 17 in the enterprise setting is both challenging and an opportunity, especially for mission-critical ecosystems. Java 17 is a long-term support (LTS) version that includes numerous enhancements over Java 8, including language syntax enhancements, improved garbage collection and memory management, enhanced security models, and modularization via the Java Platform Module System (JPMS). Nevertheless, the opportunities presented by Java 17 can be fully realised with the assistance of a well-organised migration plan that assesses risks, implements mitigation strategies, and ensures the equipping of enterprise-scale systems. This paper proposes a risk-based migration framework that is SAP-based, Java environment-specific, and identifies safe migration patterns, along with a detailed case study example to demonstrate how the workflow migration methodology works. We suggest an expedient and replicable solution that accommodates modernization.
Keywords
Java migration, Java 17, Modernization, Risk-driven framework, Backward compatibility, Enterprise Java
Cite:
Kathi, S. R. ., Joshi, P. ., Muralidhar, V. ., & Venugopalan, A. . (2026). Secure migration patterns from Java 8 to Java 17 in the mission-critical ecosystem: a risk-driven approach to modernization . Future Technology, 5(2), 297–309. Retrieved from https://fupubco.com/futech/article/view/835