Paper Title: A descriptive systematic review of contemporary MANET security research: themes, design structures, and reporting rigor
Authors: Augustina Dede Agor, Prince Silas Kwesi Oberko, Stephen Kofi Dotse, Benjamin Tei Partey, David Aboagye-Darko, Emmanuel Junior Tapany
Corresponding Author: Augustina Dede Agor (augustinadede.agor@upsamail.edu.gh )/Ghana
Abstract
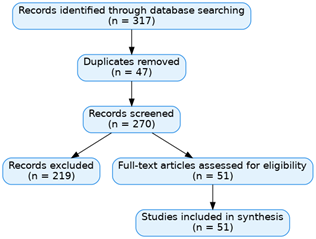
Mobile Ad hoc Networks remain vulnerable to a wide range of security threats, yet existing MANET security reviews provide fragmented insight into how recent studies frame security problems, model threats, and report design choices. This descriptive systematic review follows PRISMA guidelines and examines MANET security studies published between January and August 2025. A total of 51 studies were analyzed using a structured coding process covering security themes, attack types, defense techniques, threat modeling assumptions, detection logic, and reporting completeness. The results show convergence around a limited set of recurring attack models and reusable defense patterns. Both machine learning and deep learning, along with detection-oriented, trust-based, and optimization techniques, appear across multiple security themes rather than being confined to a single problem framing. However, threat specification, detection target definition, and trust design reporting are often incomplete or inconsistent, which limits reproducibility and cross-study comparison. Evaluation orientation, including performance metrics and experimental validation practices, is identified as an important direction for future work.
Keywords
Mobile ad hoc networks (MANETs), Systematic literature review, MANET security, Trust-based security, Threat modeling, Detection logic
Cite:
Agor, A. D., Kwesi Oberko, P. S. ., Dotse, S. K. ., Partey, B. T. ., Aboagye-Darko, D. ., & Tapany, E. J. (2026). A descriptive systematic review of contemporary MANET security research: themes, design structures, and reporting rigor . Future Technology, 5(2), 59–70. Retrieved from https://fupubco.com/futech/article/view/518